Keycard released an execution-time identity layer for coding agents, issuing short-lived credentials tied to user, agent, runtime, and task. It targets the gap between noisy permission prompts and unsafe skip-permissions workflows.

Keycard says its new system resolves a "four-part identity" for every coding session: user, agent, runtime, and task launch thread. From that, it mints credentials that are "short-lived" and scoped only to the tool call being executed, rather than leaving static API keys in local files or handing an agent broad admin access launch thread. The company’s announcement post positions policy enforcement at execution time, not just at login.
The operational pitch is to separate routine and sensitive actions. Keycard’s product details say routine actions can run autonomously, while higher-risk operations trigger real-time step-up approval. The same keycard run flow is presented as a cross-agent wrapper for Claude Code, Codex, Cursor, ChatGPT, and OpenClaw, and the thread says those policies carry across laptops, sandboxes, and CI.
The launch is targeting a failure mode many teams already recognize: approval spam and over-privileged secrets. Keycard’s problem statement says developers click "Allow" so often that prompts stop functioning as real control, while the thread argues that static keys copied into .env files leave policy and credentials "completely disconnected."
That framing lines up with early practitioner response. In one reaction, Cedric Chee summarized the model as "task-scoped credentials" plus execution-time policy, which he said gets closer to "yolo mode without giving up control." A separate discussion from swyx described identity-based authorization as the key way to move beyond the binary choice between human-in-the-loop for everything and --dangerously-skip-permissions.
Security coverage around OpenClaw intensified with a report on indirect prompt injection and data exfiltration risks, while KiloClaw published an independent assessment of its hosted isolation layers. Review your default configs and sandbox boundaries before exposing agents to untrusted web or tenant data.
 release
releaseOpenClaw shipped version 2026.3.22 with ClawHub, OpenShell plus SSH sandboxes, side-question flows, and more search and model options, then followed with a 2026.3.23 patch. Teams get a broader plugin surface, but should patch quickly and review plugin trust boundaries as the ecosystem grows.
 release
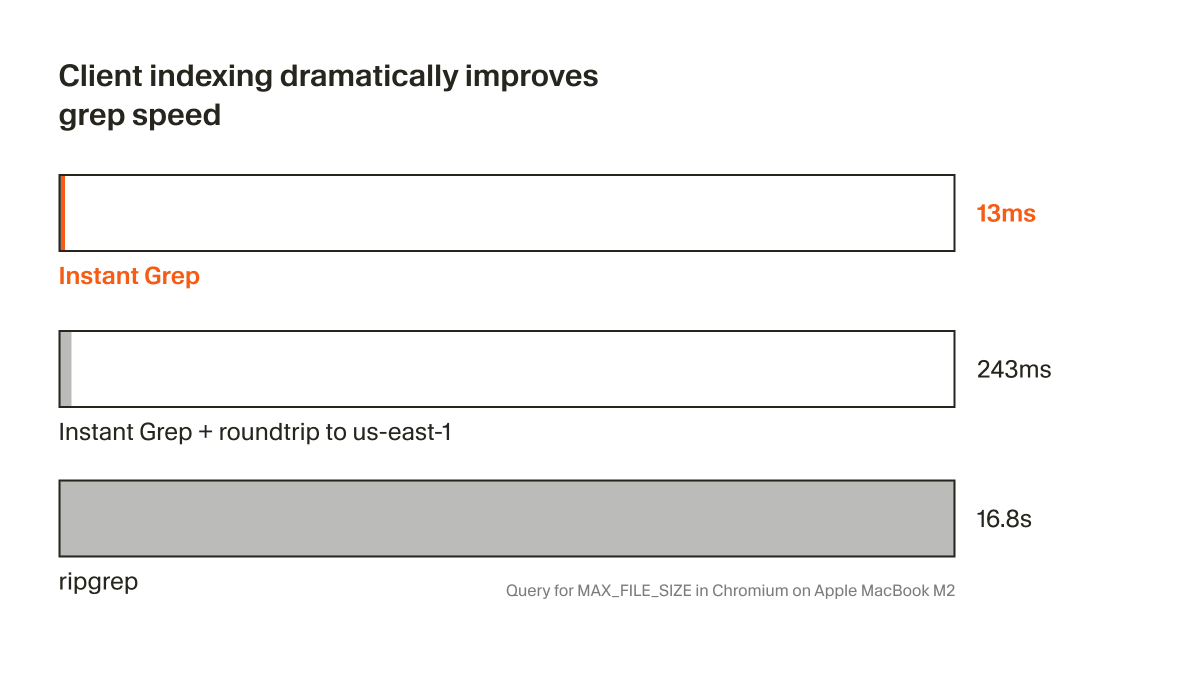
releaseCursor shipped Instant Grep, a local regex index built from n-grams, inverted indexes, and Bloom filters that drops large-repo searches from seconds to milliseconds. Faster candidate retrieval shortens the coding-agent loop, especially when ripgrep-style scans become the bottleneck.
 breaking
breakingChatGPT now saves uploaded and generated files into an account-level Library that can be reused across conversations from the web sidebar or recent-files picker. It removes repetitive re-uploading and makes past PDFs, spreadsheets, and images part of a persistent working context.
 breaking
breakingEpoch AI says GPT-5.4 Pro elicited a publishable solution to one 2019 conjecture in its FrontierMath Open Problems set, with a formal writeup planned. Treat it as an early milestone worth reproducing, not blanket evidence that frontier models can already automate math research.

Routine actions run autonomously. Sensitive operations trigger real-time step-up approval. One command, keycard run, works across Claude Code, Codex, Cursor, ChatGPT, and OpenClaw. Same policy on laptops, sandboxes, and CI.
I've been thinking about this problem a lot, so it is good to see a strong team put forward a serious solution. The real unlock for agent security is identity-based access. Give agents task-scoped credentials, enforce policy at execution time, and you finally get something close Show more
Your coding agents inherit your credentials and your permissions. No identity system in the stack can tell the difference between you and the agent acting in your name. Today: Keycard for Coding Agents 🧵