Rivet released Secure Exec, a V8-isolate runtime for Node.js, Bun, and browsers with deny-by-default permissions and low memory overhead. Agent builders can test it against heavier sandboxes for tool execution, but should verify the isolation model before replacing container or VM controls.

fs, child_process, http, dns, process, and os.Secure Exec is Rivet's new SDK for “secure Node.js execution without a sandbox,” built on V8 isolates rather than a separate container or VM. In the technical thread, Rivet says that on Node.js and Bun the isolate runs “inside the host process,” while the browser version uses Web Workers for a similar isolation model.
The company is positioning it as a lightweight runtime for untrusted code execution, especially in agent systems. Rivet's GitHub link points to the open-source repository at the GitHub repo, and the same thread lists target use cases including AI agent tool execution, MCP “Code Mode” tool execution, dev servers, plugin systems, and interactive coding playgrounds.
The practical pitch is lower overhead than heavier sandbox stacks. Rivet's benchmark claim compares Secure Exec with “best-in-class sandboxes” at 17.9 ms p99 cold start versus 3.1 s, 3.4 MB versus 256 MB of memory, and 56x lower cost on t4g.micro. It also claims “native V8 performance,” arguing that code runs through V8's normal JIT pipeline rather than through a WASM-hosted interpreter.
For agent builders, the more consequential detail is the permission model. The product thread says access to the filesystem, network, child processes, and environment variables is blocked by default and must be explicitly granted, with support for in-memory or persisted state depending on the host. That lines up with a shift in agent tooling: a practitioner thread says one experiment is removing a bash tool entirely because agents can often write JavaScript that handles the same tasks more portably, even if gaps remain around tools like git.
Vercel Labs published a stateful service emulator for GitHub, Vercel, and Google integrations instead of relying on brittle mocks. It is useful when agents or CI need deterministic auth and third-party API flows in local or sandboxed runs.
 release
releaseOpenClaw shipped version 2026.3.22 with ClawHub, OpenShell plus SSH sandboxes, side-question flows, and more search and model options, then followed with a 2026.3.23 patch. Teams get a broader plugin surface, but should patch quickly and review plugin trust boundaries as the ecosystem grows.
 release
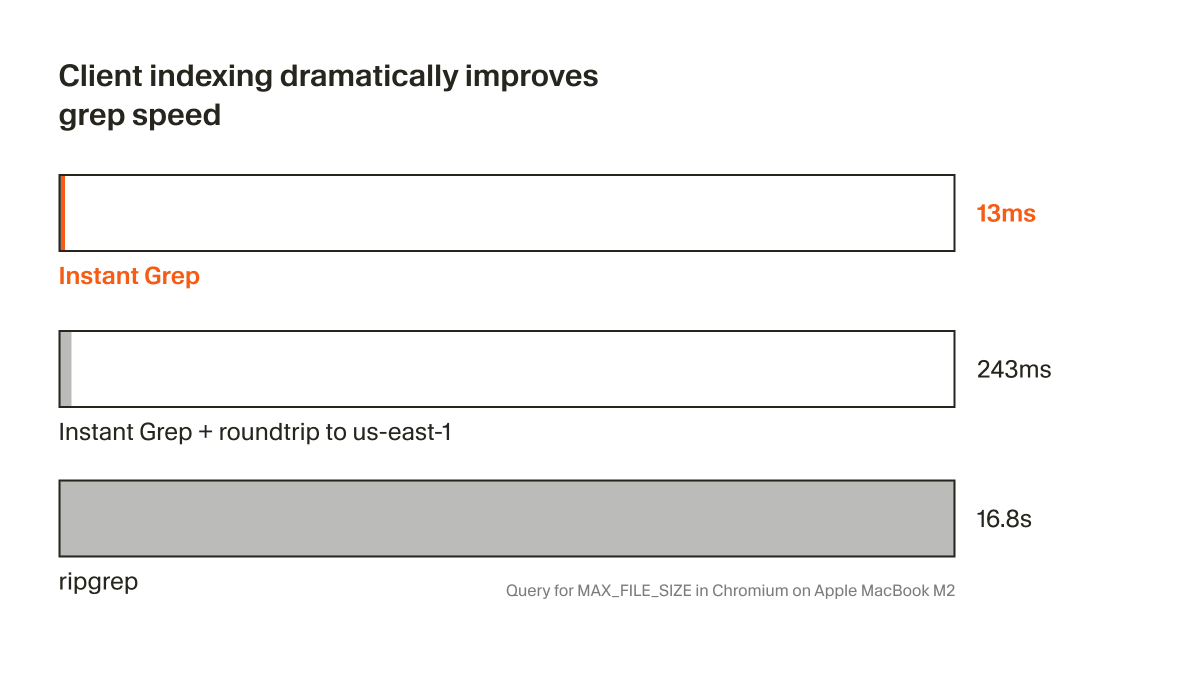
releaseCursor shipped Instant Grep, a local regex index built from n-grams, inverted indexes, and Bloom filters that drops large-repo searches from seconds to milliseconds. Faster candidate retrieval shortens the coding-agent loop, especially when ripgrep-style scans become the bottleneck.
 breaking
breakingChatGPT now saves uploaded and generated files into an account-level Library that can be reused across conversations from the web sidebar or recent-files picker. It removes repetitive re-uploading and makes past PDFs, spreadsheets, and images part of a persistent working context.
 breaking
breakingEpoch AI says GPT-5.4 Pro elicited a publishable solution to one 2019 conjecture in its FrontierMath Open Problems set, with a formal writeup planned. Treat it as an early milestone worth reproducing, not blanket evidence that frontier models can already automate math research.
Introducing the Secure Exec SDK Secure Node.js execution without a sandbox ⚡ 17.9 ms coldstart, 3.4 MB mem, 56x cheaper 📦 Just a library – supports Node.js, Bun, & browsers 🔐 Powered by the same tech as Cloudflare Workers $ 𝚗𝚙𝚖 𝚒𝚗𝚜𝚝𝚊𝚕𝚕 𝚜𝚎𝚌𝚞𝚛𝚎-𝚎𝚡𝚎𝚌