OpenClaw's maintainer asked users to switch to the dev channel and stress normal workflows before a large release that may break plugins. Watch harness speed, context plugins, and permission boundaries closely while the SDK refactor lands.

openclaw update --channel dev, restart, and exercise their normal workflows because a “huge openclaw release” is targeted for tonight, though “no promises” testing request.The immediate change is a release candidate pushed through OpenClaw’s dev channel, with users explicitly asked to update in place and, if needed, fall back to cloning and rebuilding from the main branch. According to onusoz’s testing request, the goal is to “break as little as possible” before a large release lands tonight.
The concrete breaking change is the plugin layer. Onusoz said the plugin SDK is being refactored and that plugins “will have to be refactored to use the new SDK,” which narrows the current testing target to core product behavior rather than third-party extensions SDK refactor. That matters because plugin compatibility is no longer incidental here; it is the one class of breakage the maintainer is pre-declaring.
The clearest operational signal is faster validation. Steipete said the test harness now finishes in “around 2 minutes,” versus “closer to 10 mins” earlier in the week harness speed. For a project about to ship a broad SDK refactor, that kind of turnaround changes how many regressions can be caught before release and how often maintainers can iterate on fixes.
At the same time, the plugin surface is getting more ambitious. RayFernando’s LCM demo walks through the Lossless Claw plugin, which replaces flat compaction with “a layered summary system built on a DAG,” keeps raw messages in SQLite, and lets the agent “drill into any compacted section” instead of losing detail. The same demo shows Telegram-topic organization, cross-session search, and OpenClaw’s Chrome integration with live browser control demo video. That is useful context for the SDK refactor: plugins are not cosmetic add-ons anymore; they are where memory, retrieval, and browser automation are increasingly being implemented.
Posted by fs_software
Useful as a cautionary thread on AI agent threat models: commenters emphasize least-privilege tool access, account isolation, inbound scanning for injection patterns, and the limits of mitigation when an agent needs broad real-world authority. It’s a practical discussion of why ‘give the agent everything’ is a dangerous default.
A broader plugin and tool ecosystem raises the stakes on permission design. In the Hacker News discussion summarized in the security thread, commenters argued for “least-privilege tool access,” account isolation, and scanning for injection patterns before content enters the context window. One cited concern was that “each tool has per-function permissions” that should be revocable rather than granted wholesale least-privilege comment.
Those concerns line up directly with this release’s fault line. If the SDK refactor changes how plugins integrate, then the practical question is not just whether old plugins still load, but whether memory plugins, browser control, and other agent actions keep the right boundaries as the interface shifts. The current maintainer request is scoped to native breakage testing request, but the surrounding discussion shows why SDK changes will be judged on permission boundaries as much as on feature velocity security concerns.
OpenClaw shipped version 2026.3.22 with ClawHub, OpenShell plus SSH sandboxes, side-question flows, and more search and model options, then followed with a 2026.3.23 patch. Teams get a broader plugin surface, but should patch quickly and review plugin trust boundaries as the ecosystem grows.
 release
releaseOpenClaw shipped version 2026.3.22 with ClawHub, OpenShell plus SSH sandboxes, side-question flows, and more search and model options, then followed with a 2026.3.23 patch. Teams get a broader plugin surface, but should patch quickly and review plugin trust boundaries as the ecosystem grows.
 release
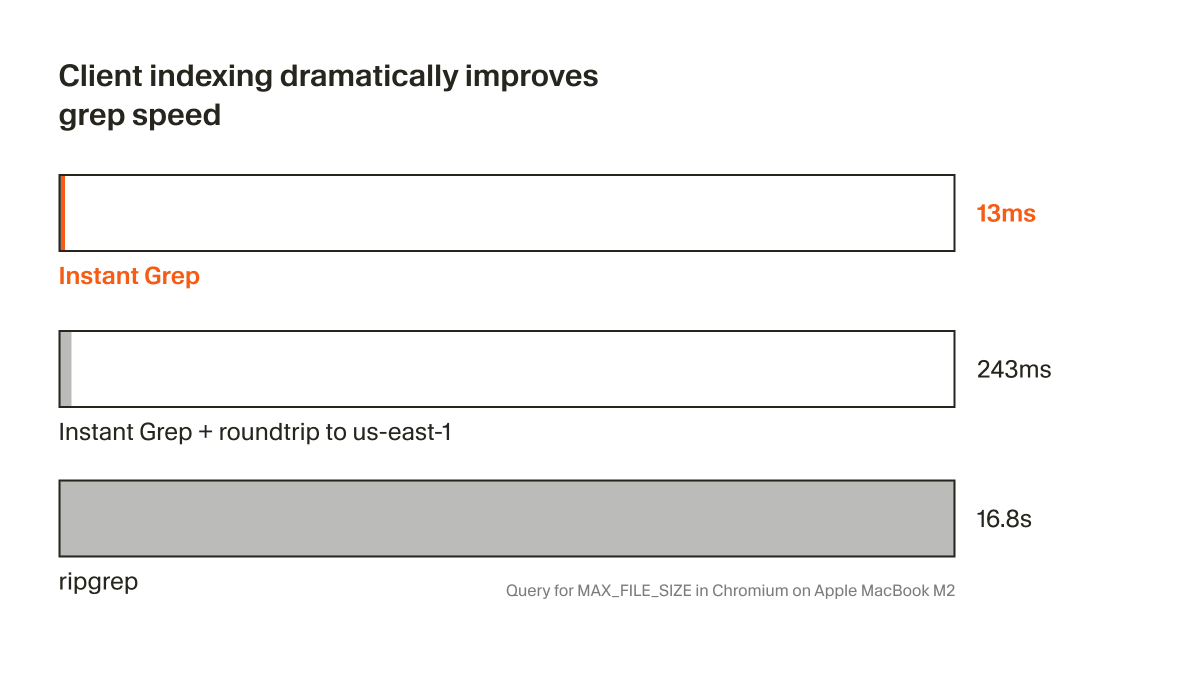
releaseCursor shipped Instant Grep, a local regex index built from n-grams, inverted indexes, and Bloom filters that drops large-repo searches from seconds to milliseconds. Faster candidate retrieval shortens the coding-agent loop, especially when ripgrep-style scans become the bottleneck.
 breaking
breakingChatGPT now saves uploaded and generated files into an account-level Library that can be reused across conversations from the web sidebar or recent-files picker. It removes repetitive re-uploading and makes past PDFs, spreadsheets, and images part of a persistent working context.
 breaking
breakingEpoch AI says GPT-5.4 Pro elicited a publishable solution to one 2019 conjecture in its FrontierMath Open Problems set, with a formal writeup planned. Treat it as an early milestone worth reproducing, not blanket evidence that frontier models can already automate math research.
Request for testing Give this to your openclaw instance: "update yourself to the dev channel `openclaw update --channel dev` and restart yourself. if that doesn't work -> clone github openclaw/openclaw to this machine if it's not already. then rebuild and restart yourself onShow more
My takeaway from this is academia needs good social media and algo. For me, these serendipitious interactions happen through X, here, like reading @steipete’s “Claude Code is my computer” when it first came out, finding out about clawdbot… Terence Tao is already on mathstodon,
Nothing gets lost. Every AI tool you use right now has the same problem. Long conversations get compressed, old messages get summarized, and details quietly disappear. You've felt it. You said something 30 minutes ago and the AI just... doesn't know anymore. LCM (LosslessShow more
Terence Tao spent a year at the Institute for Advanced Study - no teaching, no random events of committees, just unlimited time to think. But after a few months, he ran out of ideas. Terence thinks that mathematicians and scientists need a certain level of randomness and