A report and follow-up threads allege Delve issued compliance paperwork on timelines that conflict with standard SOC 2 observation windows, prompting scrutiny from engineers and vendors. Procurement teams should verify auditor names, observation periods, and current certificates instead of trusting badges at face value.

The core allegation is not just that Delve moved fast, but that the speed itself may contradict how SOC 2 Type II audits work. Orosz's thread points readers to the Substack report, which claims Delve may be using auditor relationships and processes that do not provide meaningful assurance. He frames the central question in concrete terms: how companies could appear "GDPR, SOC2, HIPAA compliant in ~a week" if the underlying controls were genuinely evaluated.
The most specific example comes from Orosz's testimonial thread and follow-up, which point to a Delve customer testimonial describing a SOC 2 Type II report issued in two weeks. That matters because, as he writes in the post, "no auditor issues this" with less than a three-month monitoring window, with six months more typical. If that timeline is accurate, the dispute is not about marketing language; it is about whether a report labeled Type II could reflect the observation period buyers expect when they review vendor security claims.
The immediate engineering reaction is skepticism toward compliance badges that lack auditable detail. In Orosz's practitioner note, someone familiar with "proper compliance work and audits" says it is "just a lie" that major certifications are typically achievable in days unless a vendor is "rubber stamping it." For teams doing security reviews, that shifts attention from badge presence to basics like the auditor name, report type, and observation period described in the paperwork.
Vendors are also clarifying whether they used Delve at all. Lovable's statement says it "is not a Delve customer," that it moved to Vanta before the current reporting, and that its SOC 2 Type II was independently audited by Prescient Assurance. A separate reaction from a widely shared reply captures the broader uncertainty: "seems like no one was actually a Delve customer....?" That does not answer the report's claims, but it shows how quickly procurement trust can erode once the audit trail itself becomes the story.
Vercel Emulate added a programmatic API for creating, resetting, and closing local GitHub, Vercel, and Google emulators inside automated tests. That makes deterministic integration tests easier to wire into CI and agent loops without manual setup.
 release
releaseOpenClaw shipped version 2026.3.22 with ClawHub, OpenShell plus SSH sandboxes, side-question flows, and more search and model options, then followed with a 2026.3.23 patch. Teams get a broader plugin surface, but should patch quickly and review plugin trust boundaries as the ecosystem grows.
 release
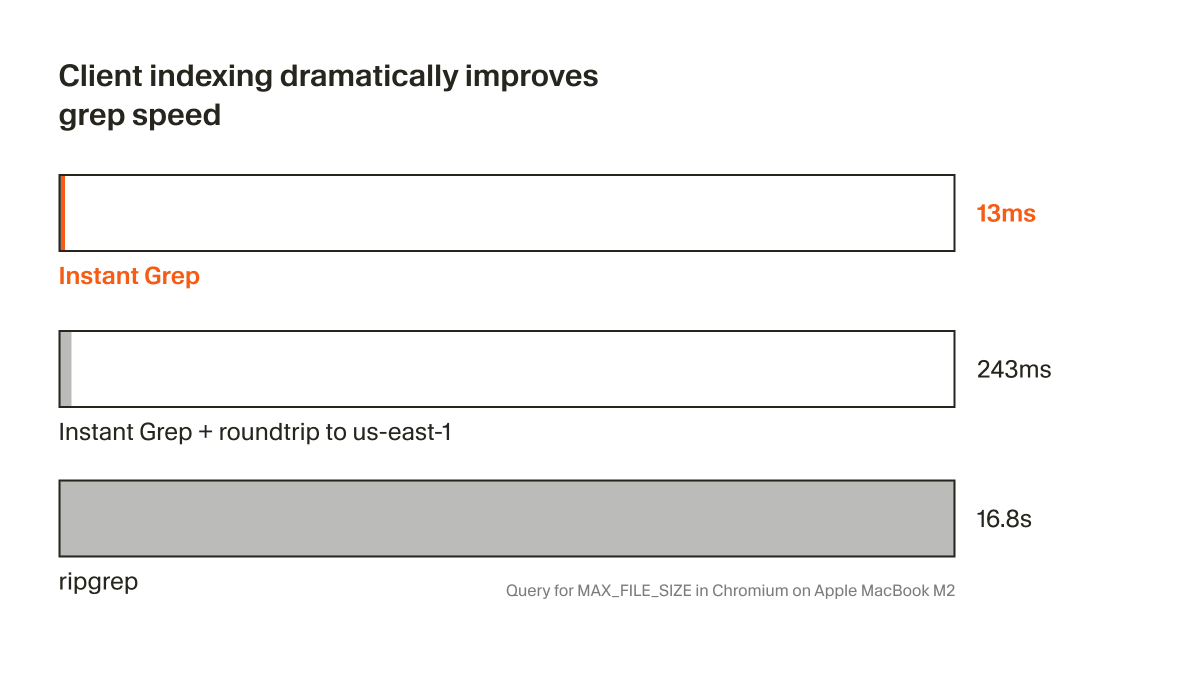
releaseCursor shipped Instant Grep, a local regex index built from n-grams, inverted indexes, and Bloom filters that drops large-repo searches from seconds to milliseconds. Faster candidate retrieval shortens the coding-agent loop, especially when ripgrep-style scans become the bottleneck.
 breaking
breakingChatGPT now saves uploaded and generated files into an account-level Library that can be reused across conversations from the web sidebar or recent-files picker. It removes repetitive re-uploading and makes past PDFs, spreadsheets, and images part of a persistent working context.
 breaking
breakingEpoch AI says GPT-5.4 Pro elicited a publishable solution to one 2019 conjecture in its FrontierMath Open Problems set, with a formal writeup planned. Treat it as an early milestone worth reproducing, not blanket evidence that frontier models can already automate math research.
Just to spell out how bad this is: - It is not possible for any US auditor to issue SOC 2 Type II certifications with less than 3 months of monitoring window (6 is typical) - Delve issued a certificate in 2 weeks!! This also means 11x (the customer) is likely not compliant...
We're aware of recent reporting about Delve’s compliance practices. Lovable is not a Delve customer. We proactively moved to Vanta in late 2025, before any of this came to light. Our SOC 2 Type II was independently audited by Prescient Assurance. We’re currently undergoing an Show more
Damning evidence suggesting that compliance certificates issued by Delve (a startup founded in 2023) are fraudlent + worthless I never understood how eg Cluely could be GDPR, SOC2, HIPAA compliant in ~a week. Now we know: they probably aren't. Just wild substack.com/home/post/p-19…
From someone who has seen up-close some (proper) complaince work and audits: It's just a lie that you can typically get to some of these major compliance certifications in days ... unless you have a vendor rubber stamping it. Which sounds like what is happening in bulk.